You Don’t Have to Be Wrong to Be a Target
“Social justice warriors” are persons or groups who actively fight for causes they feel create systemic inequity, unfairness, or disservice in our society. They advocate for people that may be marginalized or have little power or recourse. These “warriors” want to raise cause awareness, influence public opinion and acceptance, and generate changes in policies and laws.
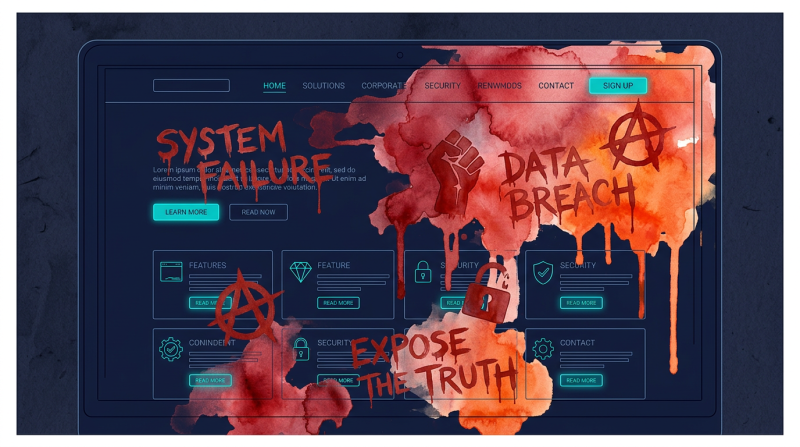
Sometimes, however, these groups can take overly dramatic steps to get their points across. Then, critics say, they focus on attention-grabbing symbolic acts rather than promoting practical results or change. Going even further, those looking for justice actually break the law by becoming cybercriminals. The activists become hackers – or Hacktivists.
Guardian CEO Chuck Smith says, “These actors want visibility — and you might be the next headline. Denial-of-service attacks. Website defacements. Leaked emails. They target brands they see as unjust or controversial.”
What do Hacktivist do, and how do they do it?
Unlike the other Bad Actors in the cyber world, Hacktivists aren’t after money, intellectual property, or are part of an international cold or hot war. They want to promote their causes by publicly disrupting, exposing or embarrassing organizations they feel are unjust. Their main attacks are:
- Distributed Denial-of-Service (DDoS). A large number of computers are used to overwhelm the target’s website or online service with traffic, causing it to slow down or crash. For DDoS, Hacktivists usually don’t break into the target directly. Instead, they build or rent “botnets” – networks of compromised computers – and command them to flood the target with traffic. However, they can also directly exploit weaknesses in the target’s servers to artificially multiply traffic.
- Hack-and-leak. This involves breaking into the target’s system to steal and then publicly publish sensitive documents and emails. The most common attack methods are through phishing or social engineering (tricking employees into giving up credentials or info), obtaining previously stolen credentials on the Dark Web, and exploiting unpatched software or web applications.
- Attackers obtain and expose private and personal identifying information of a targeted individual online, leading to harassment, identity theft or even physical harm. Like hack-and-leak above, phishing, social engineering and Dark Web searching are used. The Hacktivist gets into the target’s HR records, internal directories and email accounts to gather up identifying information.
What you need to do right now
Start here:
- Take Hacktivists seriously. Know and understand not only your public reputation and exposure, but that of partners and other companies you deal with. Remember the Aspen Forest analogy – we’re all connected. The Hacktivist’s path to their ultimate target may not be direct – and it could be through you.
- Strictly enforce MFA (Multi-Factor Authentication). This requires your employees to verify their identity using two or more proofs, such as a password plus a code sent to their phone. With MFA, stolen passwords alone can’t grant access.
- Make sure all patches and updates are current. Attackers love to find software and operating systems that have missed security updates and patches, are just plain old, or are even no longer supported by the licensor.
- Monitor the Dark Web. Continuously check whether employee usernames and passwords have been exposed or sold online.
- Go beyond traditional team training. Serious companies include ongoing gamified training and attack simulations. Employees should be able to spot social engineering and phishing scams immediately.
- Ensure you’re scanning for new vulnerabilities. Don’t lose track of all your added endpoints – laptops, desktops, servers, phones, tablets, printers, IoT devices, and more.
- Analyze yourcybersecurity budget. Most companies spend too much on reactive defenses – once a hacker is already in your system. You should invest 60 to 70 percent on proactive defenses – identifying and stopping threats before the hacktivists get in.
The Guardian Difference
Cybersecurity isn’t just defense. It’s offense – prepare, predict and protect. At Guardian, we operate from the attacker’s perspective, continuously hunting for exposure, identifying gaps, and eliminating the paths threats rely on before they’re used against you. We actively look for what’s exposed instead of simply waiting on alerts. And we monitor and test continuously to make sure you’re protected. Tools alone aren’t enough. Our experienced team protects your environment and proves that it’s working, so you can make decisions with confidence, not assumptions.