Financial Crime Gangs no longer burst in wearing masks and waving pistols to steal bags of cash. They sit behind keyboards miles away, expertly hacking your company and easily transferring your funds to their accounts.
“They’re in it for one thing: money,” says Guardian CEO Chuck Smith. “Bank logins. Wire transfers. Payroll fraud. Financial Crime Gangs are fast, focused, and often invisible. Billions are lost annually to these precision strikes.”
These gangs usually go after small- and medium-sized businesses, especially those in professional services, retail, community banks, and healthcare. Most of these companies are not cybersecurity savvy, their employees are often not well trained to spot issues, and the companies overly rely on 3rd party security providers that may not be doing all they can.
How do the Financial Crimes Gangs do it?
• Breaking in: They get in through the gaps – software and operating systems that have missed updates and fixes; are just plain old; or are still used even though they are no longer supported. They’ll also get into your systems through laptops, desktops, smartphones, and tablets that aren’t secured properly. (Exploiting vulnerabilities)
• Tricking your employees: Gangs get your employees to break their normal security habits or procedures and give out sensitive information, grant access, or click links. (Social engineering and phishing)
• Stealing identities and credentials: They steal, use and sell usernames, passwords, system access, and permissions. They’ll get you when your password protections are weak or not updated, or ex-employees’ credentials are not removed. In addition, and unfortunately, many gangs actively recruit employees to sell credentials or provide direct system access. (Identify access management)
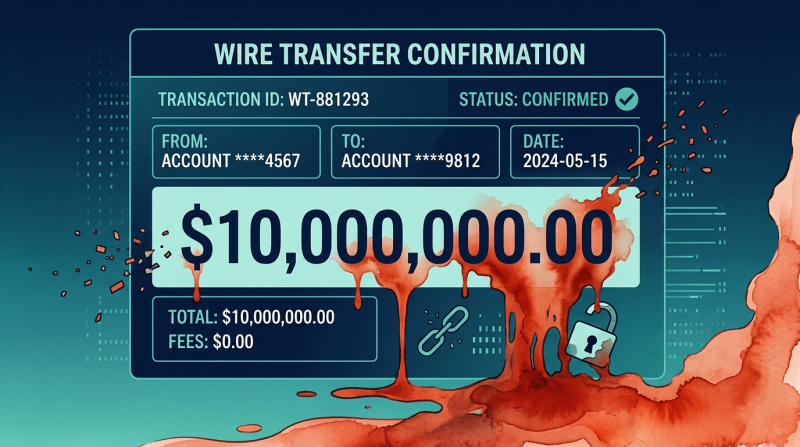
The hottest scam right now is Business Email Compromise. Attackers impersonate a company executive or trusted vendor using a look-alike email, urgently requesting money or changes to payment details. Currently millions of dollars have been lost to these crimes.
What You Need to Do … Right Now
Start here:
• Analyze your cybersecurity budget. Today, most companies spend too much on reactive defenses – once a hacker is already in your system. You should be investing 60-70 percent on proactive defenses – identifying and stopping threats before the hackers get in.
• Strictly enforce MFA (Multi-Factor Authentication). This requires your employees to verify their identity using two or more proofs, such as a password plus a code sent to their phone. With MFA, stolen passwords alone can’t grant access.
• Go beyond traditional team The once-a-year video is no longer enough. Serious companies include ongoing gamified training and attack simulations. Employees should be able to spot social engineering and phishing scams immediately and question out-of-the-ordinary or urgent requests.
• Employ behavioral analytics. This uses machine learning to spot unusual user or system activity patterns that could indicate a breach or insider threat. A simple example: a normal employee suddenly begins downloading massive files in the middle of the night.
• Constantly scour the dark web marketplaces. You need to be on the lookout for stolen employee and company credentials and other sensitive company information.
The Guardian Difference
Defender and attacker, that’s how Guardian works. Our teams work together as one defense to hunt threats, identify gaps, and stop breaches before they start. We don’t replace your IT provider or MSP agreement; we work alongside them to provide what they can’t. Why? Because cybersecurity is a hard, ever-changing environment. And anyone who tells you it’s simple, or that they already have you covered as part of other managed services, doesn’t understand today’s high-level threat landscape. We do understand, and that’s the Guardian difference.