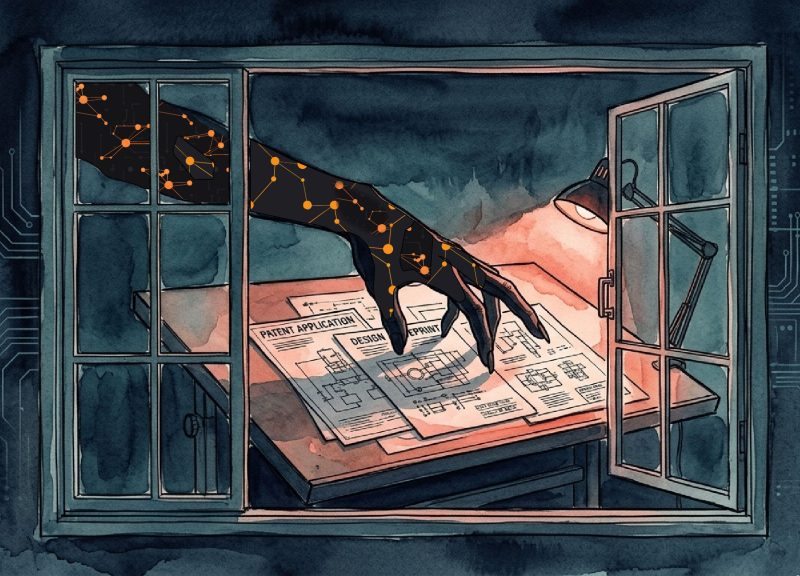
When we think of “Industrial Espionage,” we may picture a James-Bond type scaling walls, breaking into offices, and cracking safes to steal things like the microfilm for secret weapon plans. Yet, the reality of company spying is bad guys on keyboards trying to get into your systems for the information that makes your company successful.
No matter what size your business is, you may not realize the things that others would want. For example:
• Intellectual property (IP): R&D, proprietary software, designs and formulas
• Strategic plans: M&A discussions, manufacturing expansions, product roll-out dates
• Customer info: CRM data, pricing agreements, contract obligations
• Financial data: Pricing models, profit margins, banking details
“What’s your IP worth? To a competitor – maybe everything. These actors don’t crash systems. They quietly siphon trade secrets. They copy, don’t corrupt – making detection harder. They play the long game.” Chuck Smith, Guardian CEO
How Do Industrial Spies Do It?
• Phishing and social engineering: Bad actors get into your systems by tricking employees. They send emails or messages that look like they come from a boss, bank, vendor, or IT department. The message might ask the person to click on a link, open a file, or log into a fake website. When the employee does this, the attacker can (1) steal their login information and access the company’s systems and / or (2) install malware that watches activity, steals files, and collects data.
• Unpatched software weaknesses: Your company’s programs and devices require regular updates. If these updates are not installed, security holes can open up. Attackers scan the internet looking for these weaknesses and use them to enter a company’s systems.
• Hacked vendors or partners: Attackers can get in through another company that works with your company. Vendors, IT providers, or suppliers often have some level of access to your systems. If one of those partners is hacked, the attacker may use that connection to reach you – the real target.
• Insider threats: Sometimes the problem comes from inside the company. A disgruntled, bribed or blackmailed employee can steal information on purpose or share access with others. Unfortunately, this is an increasingly common event. Many times, companieswon’t remove an ex-employee’s credentials on a timely basis, making this issue worse.
• Stolen or reused passwords: Many hacks happen because attackers obtain real usernames and passwords. They may buy them on the dark web through previous data breaches.
What You Need to Do Right Now
Start here:
• Analyze your cybersecurity budget. Today, most companies spend an inordinate percentage of their budgets on reactive tools—but that doesn’t stop a threat actor from getting in—it just helps you deal with it after. Consider shifting more of your investment to proactive defenses. This includes scouring the dark web, continuously monitoring your external attack surface, and seeing what the hacker sees before any damage can be done.
• Employ behavioral analytics. This uses machine learning to spot unusual user or system activity patterns that could indicate a breach or insider threat. Simple examples: a regular 9 to 5 employee suddenly begins downloading massive files in the middle of the night; or a company computer automatically starts connecting to unfamiliar servers.
• Go beyond traditional team training. Serious companies include ongoing gamified training and attack simulations. Employees should be able to spot social engineering and phishing scams immediately.
• Constantly scour dark web marketplaces. You need to be on the lookout for stolen employee and company credentials.
• Strictly enforce MFA (Multi-Factor Authentication). This requires your employees to verify their identity using two or more proofs, such as a password plus a code sent to their phone. With MFA, stolen passwords alone can’t grant access.
The Guardian Difference
Defender and attacker – that’s how Guardian works. Our teams work together as one defense to hunt threats, identify gaps, and stop breaches before they start. We don’t replace your IT provider or MSP agreement; we work alongside them to provide what they can’t. Why? Because cybersecurity is a hard, ever-changing environment. And anyone who tells you it’s simple, or that they already have you covered as part of other managed IT services, doesn’t understand today’s high-level threat landscape. We do understand, and that’s the Guardian difference.